Virtual private networks, or VPNs
Virtual private networks, or VPNs, extend the reach of LANs without requiring owned or leased private lines. Companies can use VPNs to provide remote and mobile users with network access, connect geographically separated branches into a unified network and enable the remote use of applications that rely on internal servers.
Internet of things: Early adopters share 4 key takeaways
Getting ready to launch an IoT initiative? Read these insights and advice from early adopters in
Read Now
VPNs can use one or both of two mechanisms. One is to use private circuits leased from a trusted communications provider: alone, this is called a trusted VPN. The other is to send encrypted traffic over the public Internet: alone, this is called a secure VPN. Using a secure VPN over a trusted VPN is called a hybrid VPN. Combining two kinds of secure VPN into one gateway, for instance, IPsec and Secure Sockets Layer (SSL), is also called a hybrid VPN.
Trusted VPNs
Over the years, implementations of trusted VPNs have moved from raw private circuits leased from telecommunications vendors to private IP network circuits leased from Internet providers. The major technologies used for implementing trusted VPNs over IP networks are ATM circuits, frame-relay circuits and Multiprotocol Label Switching (MPLS).
ADVERTISING
ATM and frame relay operate at the data link layer, which is Layer 2 of the OSI model. (Layer 1 is the physical layer; Layer 3 is the network layer.) MPLS emulates some properties of a circuit-switched network over a packet-switched network, and operates at a layer often referred to as “2.5” that is intermediate between the data link and the network. MPLS is beginning to replace ATM and frame relay to implement trusted VPNs for large corporations and service providers.
Secure VPNs
Secure VPNs can use IPsec with encryption, IPsec with Layer 2 Tunneling Protocol (L2TP), SSL 3.0 or Transport Layer Security (TLS) with encryption, Layer Two Forwarding (L2F) or Point-to-Point Tunneling Protocol (PPTP). [Editors’ note: an earlier version of this article incorrectly stated that IPsec worked inside of L2TP, while the reverse is true]. Let’s go over each of these briefly.
IPsec, or IP security, is a standard for encrypting and/or authenticating IP packets at the network layer. IPsec has a set of cryptographic protocols for two purposes: securing network packets and exchanging encryption keys. Some security experts, for instance, Bruce Schneier of Counterpane Internet Security Inc., have considered IPsec the preferred protocol for VPNs since the late 1990s. IPsec is supported in Windows XP, 2000, 2003 and Vista; in Linux 2.6 and later; in Mac OS X, NetBSD, FreeBSD and OpenBSD; in Solaris, AIX and HP-UX; and in VxWorks. Many vendors supply IPsec VPN servers and clients.
Microsoft has included PPTP clients in all versions of Windows since Windows 95 OSR2; PPTP clients are in Linux, Mac OS X, Palm PDA devices and Window Mobile 2003 devices. The company has also included PPTP servers in all its server products since Windows NT 4.0.
PPTP has been very popular, especially on Windows systems, because it is widely available, free and easy to set up. However, as implemented by Microsoft, it has not always been the most secure of the secure VPNs.
Schneier, with “Mudge” of L0pht Heavy Industries, found and published security flaws in Microsoft PPTP in 1998; Microsoft quickly fixed these issues with MS-CHAPv2 and MPPE, and Schneier and Mudge published an analysis confirming the improvements in 1999, but they pointed out that the security of Microsoft PPTP still depended on the security of each user’s password. Microsoft has addressed this issue by enforcing password strength policies in its operating systems, but Schneier and Mudge still recommend IPsec rather than PPTP for secure VPNs as inherently safer.
L2TP combines ideas from PPTP and L2F, an older protocol developed by Cisco Systems Inc., to create a data link layer protocol. This provides a tunnel, but no security or authentication. L2TP can carry PPP sessions within its tunnel. Cisco implements L2TP in its routers. There are several open-source implementations of L2TP for Linux.
L2TP/IPsec combines L2TP’s tunnel with IPsec’s secure channel, which allows for easier secure Internet Key Exchange than pure IPsec. Microsoft has provided a free L2TP/IPsec VPN client for Windows 98, ME and NT since 2002, and ships an L2TP/IPsec VPN client with Windows XP, 2000, 2003 and Vista. Windows Server 2003 and Windows 2000 Server include L2TP/IPsec servers.
SSL and TLS are protocols for securing data flows at Layer 4 of the OSI model. SSL 3.0 and TLS 1.0, its successor, are commonly used with HTTP to enable secure Web browsing, called HTTPS. However, SSL/TLS can also be used to create a VPN tunnel. For example, OpenVPN is an open-source VPN package for Linux, xBSD, Mac OS X, Pocket PCs and Windows 2000, XP, 2003 and Vista, which uses SSL to provide encryption of both the data and control channels. Several vendors supply SSL VPN servers and clients.
Benefits and security risks of VPNs
A VPN can erase geographical barriers for a company, enable employees to work efficiently from home and allow a business to connect securely with its vendors and partners. A VPN is usually much cheaper to own and operate than private lines.
On the other hand, the use of a VPN can expose a company to potential security risks. While most VPNs in use are now fairly secure in and of themselves, a VPN can make it more difficult to secure the perimeter of a network properly. It is incumbent upon network administrators to apply the same security standards to computers connecting to the network via VPN as computers directly connected to the LAN.
Combining the use of two VPNs simultaneously can potentially expose one company’s network to another’s. In addition, using remote control software such as PC Anywhere, GoToMyPC or VNC in combination with a VPN can expose the company’s network to the malware present on a remote computer that is not itself connection to the VPN.
Reliability, scalability and performance of VPNs
Because secure VPNs rely on encryption and some of the cryptographic functions used are computationally expensive, a heavily used VPN can load down its server. Administrators typically manage the server load by limiting the number of simultaneous connections to what the server can handle.
When the number of people attempting to connect to the VPN suddenly peaks, for example, during a storm that disrupts transportation, employees may find themselves unable to connect because all VPN ports are busy. That gives administrators motivation to make key applications work without requiring the VPN, for instance, by setting up proxy servers or Internet Message Access Protocol servers to enable employees to access e-mail from home or from the road.
Deciding between IPsec and SSL/TLS for a given scenario can be complicated. One consideration is that SSL/TLS can work through a NAT-based firewall; IPsec cannot, but both protocols work through firewalls that do not translate addresses.
IPsec encrypts all IP traffic that flows between two computers. SSL/TLS is specific to an application. SSL/TLS uses expensive asymmetric encryption functions to establish a connection, and more efficient symmetric encryption functions to secure a running session.
In a real-world remote application, administrators may decide to mix and match protocols for the optimum balance of performance and security. For example, clients might connect to a Web-based front end through a firewall using a browser secured by SSL/TLS; the Web server might connect to an application server using IPsec; and the application server might connect to a database server across another firewall using SSL.
The scalability of VPNs can sometimes be improved by the use of dedicated server hardware. To cover that, however, we’d have to wade through the competing claims of VPN vendors: perhaps a subject for another day.
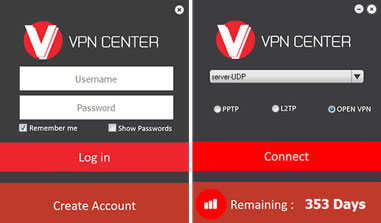
Buy VPN
|
Compatible with all Windows versions OPEN VPN – L2TP/IPSEC VPN – PPTP VPN – SSTP VPN |
Download SoftwarePreview Application Vpncenter |
Buy Vpn .The Best vpn services |
 |