VPN ( Virtual private network )
What is a Virtual Private Network (VPN)?
A Virtual Private Network (VPN) is a secure and separate network, which let users connect to the internet through an encrypted tunnel bypassing their public network and securely transfers their internet data packets through it, VPN is just like a firewall in computers which protects you from the local area network (LAN) attacks, VPN works as an online firewall to protect your from all the cyber hazards and attackers, to use a VPN an active connection is mandatory. VPNs are a mix of various technologies which;
- Gives you Anonymity over the internet
- Hides your IP address and internet activities from your ISP and other snoopers like government surveillance and security agencies provide internet security and privacy
- Let you bypass geo-restrictions and access all the blocked websites when you are outside your country
- Gives you absolute protection from cyber attackers like hackers, spammers, etc.
- Let you share files using P2P file sharing websites
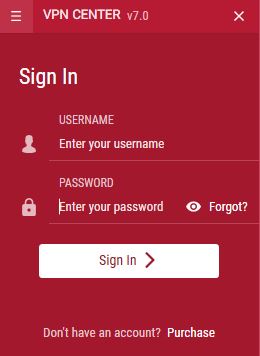
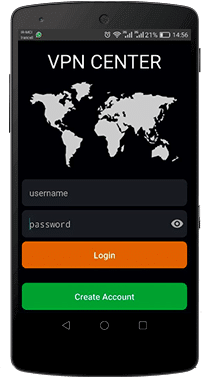
What is VPN for Mobile?
VPNs are also installed and used in all smartphones to protect them from cyber attacks and threats like hacking, spamming, snooping by NSA and government security and surveillance agencies etc. and provide them full anonymity while browsing the internet on their mobile devices. Not on the VPN provide the mobile user’s anonymity and privacy but also gives them power to access all the blocked content due to censorship laws and geo-restrictions in different countries. All the latest smartphones available in the market these days comes with the built-in VPN support interface, which makes them compatible with all the major VPN Apps for smartphones operating system like Android, iOS, etc.
Security
Over Billion of people around the world use the internet all around the world, according to Wikipedia the largest number of internet users are in China with a total of 721,434,547 users till 2104 by now it must have been increased which ranked China the 1st in the list of countries by number of Internet users followed by the India, USA etc. these figures include the internet users from all the device like computers, PC, mobile phones etc. with this huge numbers of people using the internet from all around the world they are also exposed to the potential threats of cyber crimes like hacking, spamming etc. according to a report by Identity Theft Resource Center (ITRC) last year in 2015, 781 hacking incidents were recorded which resulted in data security breach which is very alarming. Hackers and spammers are also getting stronger by the enhancement in the technology as they are exploiting it to fulfil their evil intentions which harm many individuals and businesses as Identity theft, Financial accounts access, data theft etc. and all these are done for two reasons; for money and sometimes to steal highly confidential information, and the cyber criminals usually do it by snooping into the connection by finding any flaw in the security barrier from where they get the chance to exploit the user’s information and hack the information through the network. A VPN provides you protection against all such cyber attacks by providing you a secure and private connection which is away from all the snooping eyes on the network and enhance your security level so it is harder for any attacker to bypass it. However, not all VPN services are secure enough some VPNs can be another problem for you as they keep the log of users’ data which can be a death of the main purpose of using a VPN, that is security.
Privacy from Snooping
In this era of post-Snowden, who doesn’t know about the government and security agencies spying on the user’s’ internet activities and compel the ISPs to log the user’s’ data so it can be monitored and shared? This is done by most of the developed countries like the US, UK, Australia, Canada, New Zealand etc. Security agencies claim this as an act of state security against terrorism and other cyber crimes, but people are reacting towards it in a very different manner and most of them think it violates user’s privacy laws, as the government and security agencies have been doing it for years without the consent of people, before it was leaked by Snowden. A VPN enhances your privacy by blocking these snooping by anyone either it is your ISP or the government and security agencies, it creates a virtual encrypted tunnel to route all your internet data in an unreadable form and connect you anonymously to the internet which saves you from the spying eyes.
Secure Privacy with VPN
The VPN security model provides:
- Confidentiality such that even if the network traffic is sniffed at the packet level (see network sniffer and Deep
packet inspection), an attacker would only see encrypted data - Sender authentication to prevent unauthorized users from accessing the VPN
- Message integrity to detect any instances of tampering with transmitted messages
Secure VPN protocols include the following:
- Internet Protocol Security (IPsec) as initially developed by the Internet Engineering Task Force (IETF) for IPv6,
which was required in all standards-compliant implementations of IPv6 before RFC 6434 made it only a recommendation. - This standards-based security protocol is also widely used with IPv4 and the Layer 2 Tunnelling Protocol.
Its design meets most security goals: authentication, integrity, and confidentiality. - IPsec uses encryption, encapsulating an IP packet inside an IPsec packet. De-encapsulation happens at the end of the tunnel, where the original IP packet is decrypted and forwarded to its intended destination.
- Transport Layer Security (SSL/TLS) can tunnel an entire network’s traffic (as it does in the OpenVPN project and
SoftEther VPN project) or secure an individual connection. A number of vendors provide remote-access VPN capabilities through SSL. An SSL VPN can connect from locations where IPsec runs into trouble with Network Address Translation and firewall rules. - Datagram Transport Layer Security (DTLS) – used in Cisco AnyConnect VPN and in OpenConnect VPN] to solve the issues SSL/TLS has with tunnelling over UDP.
- Multi Path Virtual Private Network (MPVPN). Ragula Systems Development Company owns the registered trademark “MPVPN”.